Secure IT Infrastructure 4018686200 Online

The concept of Secure IT Infrastructure 4018686200 Online is pivotal for modern enterprises. It emphasizes the necessity of safeguarding sensitive data and ensuring operational resilience against cyber threats. By integrating advanced security measures, organizations can fortify their digital environments. However, the implementation process presents unique challenges. Understanding these intricacies is crucial for businesses aiming to bolster their cybersecurity posture and maintain stakeholder trust. What are the specific features and strategies that can enhance this infrastructure?
Why a Secure IT Infrastructure Is Essential for Your Business
As businesses increasingly rely on digital operations, the necessity for a secure IT infrastructure becomes paramount.
A robust IT framework ensures data protection against cyber threats, thereby safeguarding sensitive information. Moreover, it enhances business continuity by minimizing downtime during disruptions.
Key Features of the Secure IT Infrastructure 4018686200 Online
A secure IT infrastructure encompasses several critical features designed to protect organizational assets and ensure operational integrity.
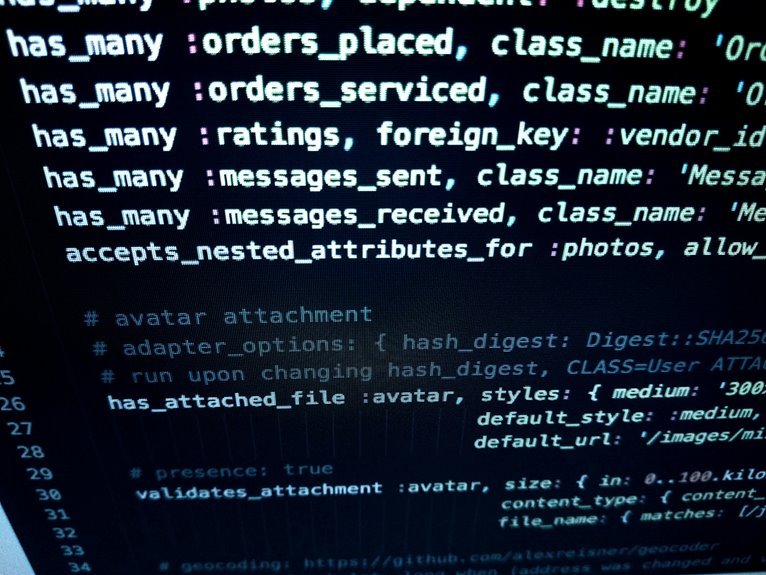
Key components include robust cloud security measures that shield data from unauthorized access, alongside advanced data encryption techniques that secure information during transmission and storage.
These features collectively enhance resilience against cyber threats, fostering an environment where organizational freedom and data integrity coexist harmoniously.
How to Implement Secure IT Infrastructure 4018686200 for Your Company
Implementing a secure IT infrastructure requires a systematic approach that encompasses various strategic measures tailored to the unique needs of the organization.
Key actions include establishing network segmentation to isolate sensitive data and systems, while implementing robust access controls to ensure that only authorized personnel can access critical resources.
This framework enhances security posture, mitigates risks, and fosters organizational resilience against potential cyber threats.
Common Challenges in Cybersecurity and How Does This Solution Address Them?
While organizations strive to enhance their cybersecurity posture, they often encounter a range of challenges that can undermine their efforts.
Phishing attacks and data breaches remain prevalent threats, exploiting human vulnerabilities and system weaknesses.
The implementation of Secure IT Infrastructure 4018686200 directly addresses these issues by providing robust defenses, continuous monitoring, and employee training, thereby reducing the risks associated with these common cybersecurity challenges.
Conclusion
In conclusion, the necessity for a secure IT infrastructure is underscored by the ever-evolving landscape of cyber threats. The Secure IT Infrastructure 4018686200 Online embodies a comprehensive approach, integrating advanced security features to mitigate risks. By addressing common cybersecurity challenges, it not only protects sensitive data but also enhances organizational resilience. This reinforces the theory that a proactive security posture is essential for maintaining business integrity and fostering stakeholder confidence in an increasingly digital world.